Why security fails
Thinking more deeply about physical security and how to implement it
Who says we don’t do good ‘ol fashioned heists anymore? The world may be going digital, and crypto is the easiest way to steal and move money, but bandits are still out there robbing Scrooge McDuck safes full of cash. Just ask GardaWorld. On Easter Sunday 2024, thieves broke into their facility in Los Angeles, and made off with more than $20 million in cash. That’s the kind of take you expect to see in a Netflix series. They came through the roof, bypassed alarms, opened the safe, and vanished without a trace. No alarms went off. No police were dispatched. The facility had a history of false alarms, so by the time a real breach occurred, everyone was asleep at the switch.
Security is like an onion
The biggest gaps in security systems don’t usually come from obvious blind spots with no coverage at all. They come from using the wrong type of security measure in the wrong place. Take police alarms, for example. Many companies, like GardaWorld, use alarms that alert local law enforcement directly, triggering a response within some (hopefully reasonable) amount of time. But what exactly are these alarms meant to do? Are they intended to deter criminals by signaling that police will be notified? Are they meant to stop criminals from escaping by ensuring officers arrive quickly enough? Or are they primarily about getting police to the scene fast enough to begin an effective investigation?
These are very different goals, and if you haven’t clearly thought through which one you’re relying on, you may be disappointed by the results. The key is to treat your security system like an onion. Let’s peel back those layers to understand what matters, and when.
The Layers
Most people think of security systems in terms of what they do. “Cameras see images,” “motion detectors detect motion,” “keys grant and prevent access,” etc. Instead, I recommend thinking of security in terms of why it exists. So I split up security tools and procedures into the following categories:
Deter
Deny
Delay
Respond
Investigate
1. Deter
A lot of people think deterrence is just the sum of all other security layers: if you have strong deny, delay, respond, and investigate capabilities, attackers won’t even try. But if that were true, the best security would be a billboard outside your building spelling out exactly how tight your defenses are. No secrets, just confidence.
But that’s not how deterrence really works. In international security, deterrence strategy is often broken into two categories:
Convince the adversary they will fail.
Convince them that success will cost too much.
Most companies don’t have the resources to guarantee failure for every possible adversary. But they can still deter by showing that any attempt—win or lose—is going to be painful.
Think about dogs. They don’t block doors. They don’t write reports. But they’re excellent deterrents because they raise the perceived cost of action. Barbed wire, electric fences, visible firearms—these aren’t airtight defenses, but they signal pain, hassle, or risk. That’s the deterrence category most businesses should be thinking in: not “how do I stop you,” but “how do I make you not want to start.”
2. Deny
Denial refers to measures that make unauthorized physical access effectively impossible under normal threat conditions. If a barrier can be moved, broken, or circumvented with tools readily available to an adversary, it does not truly deny—it merely delays. True denial depends on permanence, durability, and appropriateness to the likely threat.
A concrete wall may not stop a military attack, but it is sufficient for most criminal threats. In contrast, the GardaWorld case, where thieves entered through a self-cut roof opening, illustrates that poorly secured architectural elements can invalidate other robust protections. Thus, denial must be proportional to the asset’s value and the adversary’s capabilities. Ask: What are you protecting? Who are you protecting it from? What tools or methods might they use?
Some common examples of denial include:
Reinforced concrete barriers or walls that cannot be removed or bypassed without heavy equipment
Ballistic-rated doors and windows designed to withstand forced entry or gunfire
Bollards or anti-vehicle barriers anchored to prevent ramming attacks
Electronic access systems (e.g., biometric or card readers) embedded in hardened enclosures
Roof reinforcement or intrusion detection systems in areas vulnerable to vertical entry
By contrast, items like chain-link fences, unreinforced drywall, and simple locks are generally delay mechanisms. They serve to slow an attacker and buy time for detection and response but do not inherently prevent access. To ensure actual denial, these systems must be layered with structural integrity and aligned with a well-understood threat model.
3. Delay
Most common security measures are delay mechanisms, not true barriers. That doesn’t make them useless. It just means they need to be understood and used correctly.
A while back, I locked myself out of my house. My dog was whining inside, and I had no spare key. The locksmith arrived and drilled through my supposedly high-security deadbolt using a diamond-tipped bit. It took about 60 seconds. There was noise, some smoke, and then the door popped open. That expensive deadbolt bought me exactly one minute.
And that might be enough if the delay triggers other systems. A minute could be time for an alarm to sound, a camera to activate, or law enforcement to be notified. If you layer hardened entry points like a metal gate with other reinforced doors and internal locks those 60 seconds could stretch into 15 minutes or more. But make no mistake: delay is not denial.
Denial means preventing access entirely under normal threat conditions with reinforced walls, vault-grade enclosures, or locked server racks inside a controlled facility. Most physical security tools like padlocks, doorknobs, even fences simply slow people down. If you understand that, you can design a system that uses delay to your advantage. If you don’t, you’re building on a false sense of security.
Delaying an attacker isn’t just about slowing their entry. It’s also about disrupting their exit. Depending on what you’re protecting, it may make sense to implement lockdown procedures that isolate or trap the intruder. Escape delay can be just as valuable as entry delay, especially when response time is a key part of your defense.
For example, some schools have dropdown gates in hallways that can be activated to restrict an attacker’s movement within the building, channeling them into specific zones or preventing them from reaching high-risk areas. Similarly, some retail environments use doors that automatically lock from both sides once triggered. If a thief grabs goods and heads for the exit, they may find themselves locked inside, trapped with the evidence until help arrives.
These strategies work best when combined with detection and response systems. Slowing an attacker’s retreat can buy valuable minutes for first responders or internal security to act. And in some cases, it can be the difference between a loss and an arrest.
4. Respond
You’ll notice I don’t include “alert” as one of the core security functions. That’s because an alert is not a function itself—it’s the signal that activates the others. Alerts act like the nervous system of a security framework: they trigger action but aren’t action in and of themselves. Silent alarms, phone calls, and automated notifications are examples of alerting mechanisms that initiate a response. The effectiveness of a security response depends on how quickly it happens and how much human involvement it requires.
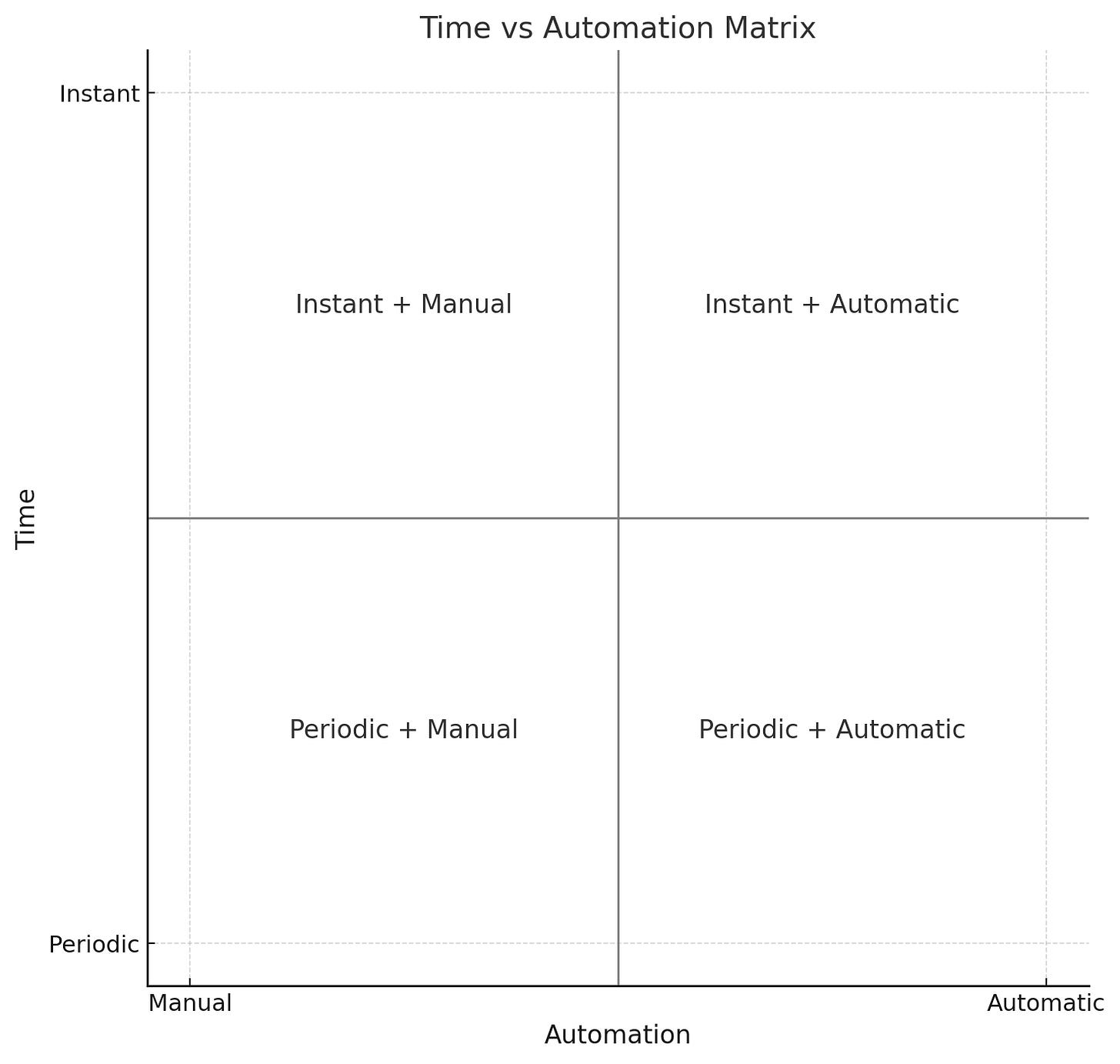
One useful way to think about response capability is on a two-axis grid. The X-axis spans from “manual” to “automatic.” The Y-axis spans from “periodic” to “instant.” These axes help map the kind of response that’s required, based on what’s being protected and how urgently action is needed.
Instant and Automatic (top right): A motion-sensor light. Motion triggers an immediate lighting or alarm response. No human involvement.
Periodic and Automatic (bottom right): A silent alarm routed to law enforcement. It triggers automatically but relies on an external party to respond with some time delay.
Instant and Manual (top left): Ok so nobody can have an instant manual response, but the closest is if you think about a security guard reacting in real-time to a visible incident. No automation, but high responsiveness.
Manual and Periodic (bottom left): A CCTV system with footage reviewed after the fact. A human needs to monitor or analyze the feed, often with delay.
5. Investigate
Many people assume that once law enforcement is notified, they will fully investigate any security incident. But even in jurisdictions with competent and trustworthy authorities—a privilege not everyone can count on—law enforcement’s goals are not necessarily aligned with yours. Their primary role is to investigate crimes and pursue prosecutions. They might keep you informed, or they might not. They might share findings, or they might not. They are not responsible for helping you understand how the incident happened or how to prevent it from happening again. That responsibility lies with you. It’s up to you to investigate the failure points in your own systems and take steps to ensure it doesn’t happen again.
Instead of trying to play detective or frantically searching the internet to find the person who stole from you, take a step back and accept a hard truth: even the best security systems fail. Failure is not a possibility—it’s an eventuality. That’s why your security setup needs built-in redundancies and the ability to reconstruct events after the fact.
This is a common example of security principles being misapplied. Take CCTV: it’s often treated as a deterrent, but it’s not particularly effective at deterring, denying, delaying, or responding to an incident. What it does well is help you investigate what happened. But that only works if it’s set up correctly. Make sure your footage is backed up. If your cameras run on WiFi, you should get alerts when the signal drops, because that might not be an accident.
There are many tools that support investigation, depending on what you’re protecting. Banks use dye packs. Facial recognition systems are getting cheaper. In insider threat scenarios, keycard swipes and access logs can help you retrace someone’s movements. These aren’t just nice-to-haves—they’re essential if you want a chance at understanding how your system was breached and making sure it doesn’t happen again.